Vulnerability Assessment and Penetration Testing (VAPT) Services – Direct-I
In today’s interconnected world, cybersecurity is no longer optional—it’s essential. With cyberattacks becoming increasingly sophisticated, businesses of all sizes face the constant threat of data breaches, ransomware, and other malicious exploits. At Direct-I, we provide comprehensive Vulnerability Assessment and Penetration Testing (VAPT) services designed to uncover weaknesses in your IT infrastructure and help you build stronger defenses before attackers strike.
Types of Vulnerability Assessment and Penetration Testing
Web Application
Mobile Application
API
Network
Cloud
iOT
Understanding VAPT: A Complete Approach to Cybersecurity Testing
Vulnerability Assessment (VA)
- Automated Scanning: Using advanced tools to detect outdated software, misconfigurations, unpatched systems, open ports, and known vulnerabilities.
- Risk Categorization: Classifying discovered vulnerabilities based on severity, potential impact, and ease of exploitation.
- Prioritization: Helping you focus on high-risk vulnerabilities that require immediate attention.
Penetration Testing (PT)
Vulnerability Assessment focuses on identifying potential flaws and security gaps in your systems, networks, applications, and devices. This step involves:
- Simulate Real Threats: Recreate tactics used by hackers, such as brute-force attacks, SQL injections, phishing, privilege escalation, and lateral movement.
- Exploit Vulnerabilities Safely: Test whether identified flaws can actually be breached without harming your systems or data.
- Measure True Business Risk: Provide you with clear evidence of how attackers could compromise your assets, steal data, or disrupt operations.
Why VAPT is Crucial for Your Business
Cybersecurity breaches can have devastating consequences—not only financially, but also in terms of reputation and customer trust. Here’s why you need VAPT:
- Stay Ahead of Hackers: Identify weaknesses before cybercriminals find and exploit them.
- Protect Sensitive Data: Secure personal information, financial data, and intellectual property.
- Minimize Downtime: Prevent costly business interruptions caused by ransomware or system breaches.
- Meet Industry Compliance: Fulfill mandatory requirements for standards like ISO 27001, PCI-DSS, HIPAA, GDPR, and others.
- Strengthen Stakeholder Confidence: Show clients, partners, and investors that you take cybersecurity seriously.

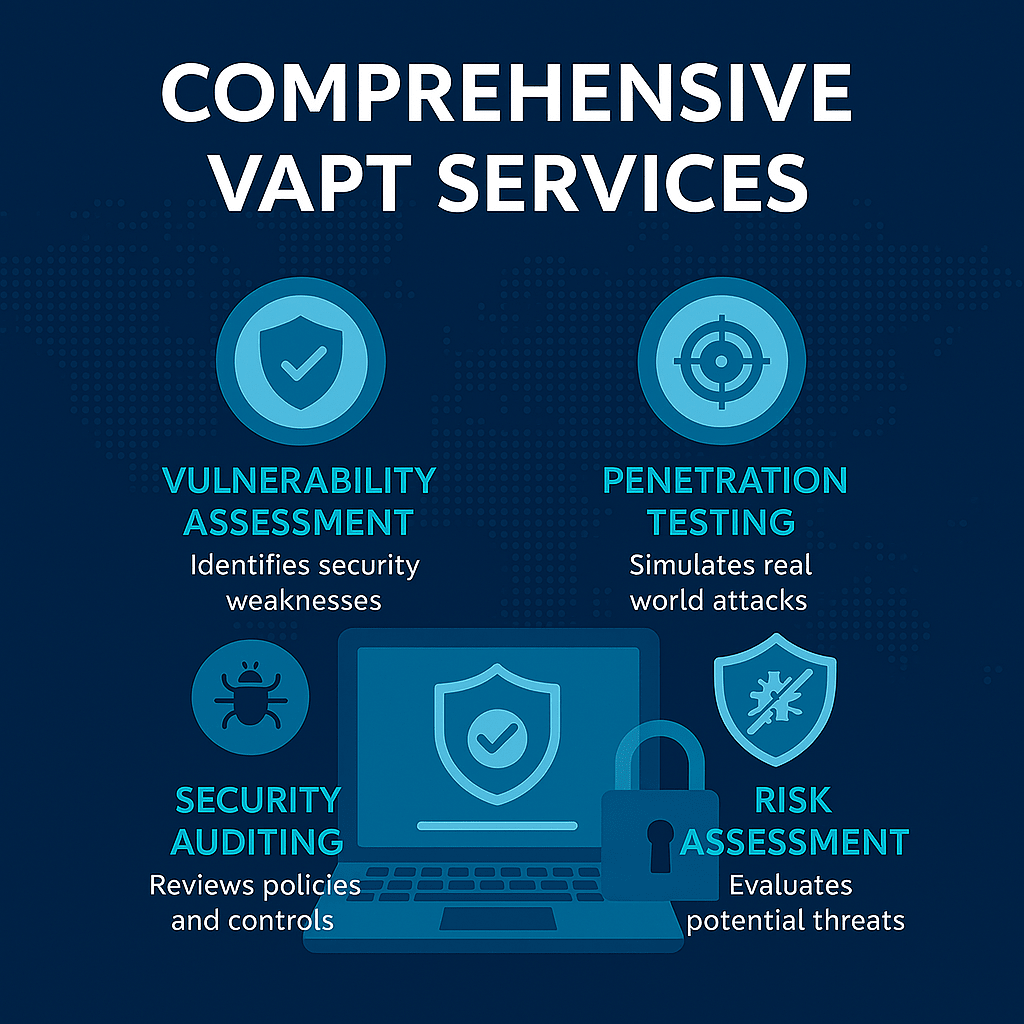
Our Comprehensive VAPT Services
At Direct-I, we offer a broad range of VAPT solutions tailored to different areas of your IT environment:
- Network Vulnerability Assessment: Detect configuration flaws, weak firewalls, and unpatched systems within your internal and external networks.
- Web Application Security Testing: Identify coding flaws, injection attacks, cross-site scripting (XSS), and other web-based vulnerabilities.
- Mobile Application Penetration Testing: Ensure your mobile apps are secure against data leaks and unauthorized access.
- Cloud Infrastructure Security Testing: Analyze your cloud setup for misconfigurations, insecure APIs, and access control weaknesses.
- Wireless Network Assessment: Test Wi-Fi networks for potential exploitation points and rogue access points.
- Social Engineering Assessments: Evaluate employee awareness through phishing simulations and targeted attacks.
- Post-Remediation Testing: Verify that all identified vulnerabilities have been effectively patched and no new risks have been introduced.
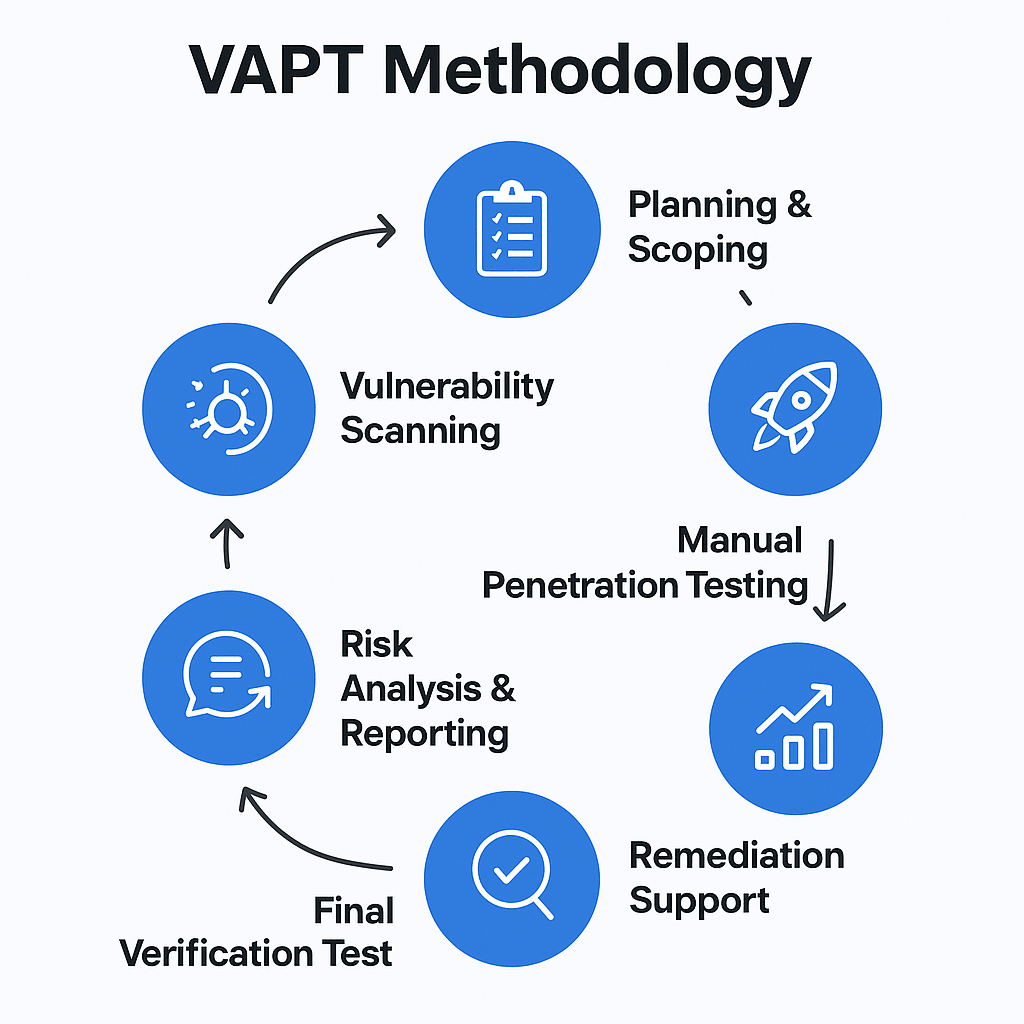
Our Proven VAPT Methodology
We follow a structured, industry-standard approach to ensure accurate, reliable, and actionable results:
- Initial Consultation & Scoping: We understand your systems, objectives, and potential threat landscape.
- Information Gathering: Collect relevant data about your network, applications, and architecture.
- Vulnerability Scanning: Perform automated scans to detect known weaknesses.
- Manual Penetration Testing: Ethical hackers simulate real-world attacks to validate the findings and discover hidden vulnerabilities.
- Risk Analysis & Detailed Reporting: Provide a comprehensive, easy-to-understand report with severity ratings, evidence of exploitation, and step-by-step remediation guidelines.
- Remediation Support: Work with your team to fix the vulnerabilities effectively.
- Final Verification: Re-test systems to confirm that all risks have been mitigated.
This methodology ensures that you not only know where your weaknesses are but also how to fix them effectively and prevent future attacks.

Why Choose Direct-I for VAPT?
- Certified Security Experts: Our team consists of professionals certified in CEH, OSCP, CISSP, and other global cybersecurity standards.
- Comprehensive Approach: We combine automated tools with manual testing to uncover even the most complex vulnerabilities.
- Actionable Insights: Our reports go beyond technical jargon, offering clear guidance for both technical and business decision-makers.
- Safe and Ethical Testing: All testing is performed in a controlled, non-disruptive environment.
- Continuous Support: We don’t stop at reporting vulnerabilities—we help you secure your business long-term.
- Cost-Effective Solutions: Enterprise-grade security services at competitive pricing.
